User Tools
Sidebar
Add this page to your book
Remove this page from your book
This is an old revision of the document!
Table of Contents
Security
Security is increasingly important. As PMA.core has been deployed in increasingly complex scenarios over the years, its security features have evolved, too.
Security pertaining to root-directories is situated at two levels:
- Security features that enable root-directories to access content, such as:
- Configure public/secret key combinations for S3 resources
- Configure account credentials to be used when accessing a UNC network resource path
- Prevent users from access mounted content through root directories that they are or are not allowed to do
- Define Access control lists
The following paragraphs elaborate on these respective subjects:
Accessing secured content
Based on the type of data storage that a root directory's mounting point refers to, the configuration offers different options:
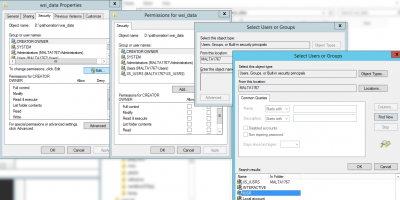
Local hard disk entry points
If you want to expose a local folder on the server's hard disk as a root directory in PMA.core, the simplest way to do this is by giving the IIS user account access rights to the folder using the Windows Explorer:
Network storage (UNC paths)
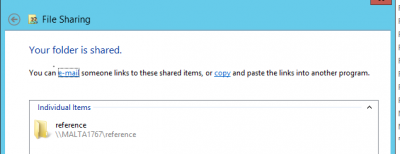
Pathomation runs under a certain application pool. This application pool is associated with a user identify, which may not have access to the network path that you try to access. Giving access for the application pool to access the network resource may be difficult for a variety of reasons.
If you can't immediately access the network path with default (i.e. application pool) credentials, you can provide additional information.
In the case below we've created a dedicated pma_read user that is permitted to acces the shared \\MALTA1767\reference path:
S3 storage
Azure storage
Public vs private
Public root directories can be accesses by anybody who is a registered user in the PMA.core user repository.
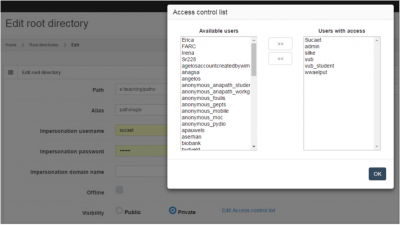
Private root directories are only accessible by those who have been explicitly given access to be allowed to access the folder through the directory's access control list.
Access control lists
Once marked private, you can select what users are allowed to see the content of the root directory, and which ones aren't: Do this by pressing the “Edit access control list” link after you selected the “private” option: